Penetration Testing Services
Security Assessment Services
Vulnerability Assessment
Identify and evaluate security weaknesses in internal network and infrastructure.
Penetration Testing
Validate the identified vulnerabilities in the organisation to upgrade the overall cyber security posture .
Red Team Assessment
Enhancing the defensive security with advanced persistent threats.
Spear Phishing Assessment
We check the awareness of the people towards cyber security policies.
Web App Pentesting
Identify and evaluate security weaknesses in enterprise web applications with our SAST and DAST approach.
Secure Code Review
Find and fix out issues inside in the code blocks with our SAST servies.
Infrastructure Pentesting
Secure the enterprise's Internal and External infrastructure including Wireless & Wired networks, VPN, Firewall, Endpoint Security Products, Active Directory , Database etc with our team .
Mobile App Pentesting
Maturing the enterprise mobile application with our customised mobile pentesting solutions.
Thick Client Pentesting
Get ready to mature the security weaknesses in the Desktop applications.
ICS SCADA Pentesting
Protect the ICS / SCADA environments with our tailored cyber security solutions
IoT Pentesting
Know the loopholes in the Hardware devices and Fix the issues with our cyber warriors.
Cloud Pentesting
We find and fix the issues in the enterprise's Internal and External Cloud infrastructure including orchestration, IAAS , PAAS and SAAS environments
Security Configuration Review
Addressing the baseline security and provide best hardening guidelines worldwide.
Web Api Pentesting
Assessing and safeguarding the core functionality of web applications through both automated and manual methods is the central focus.
Blockchain Pentesting
Evaluating blockchain security via vulnerability testing to prevent potential breaches.
Web3 Pentesting
Securing Web3 by probing and addressing vulnerabilities in decentralized apps and protocols.
DevSecOps Solutions
Strengthening software development through security-focused testing in DevSecOps.
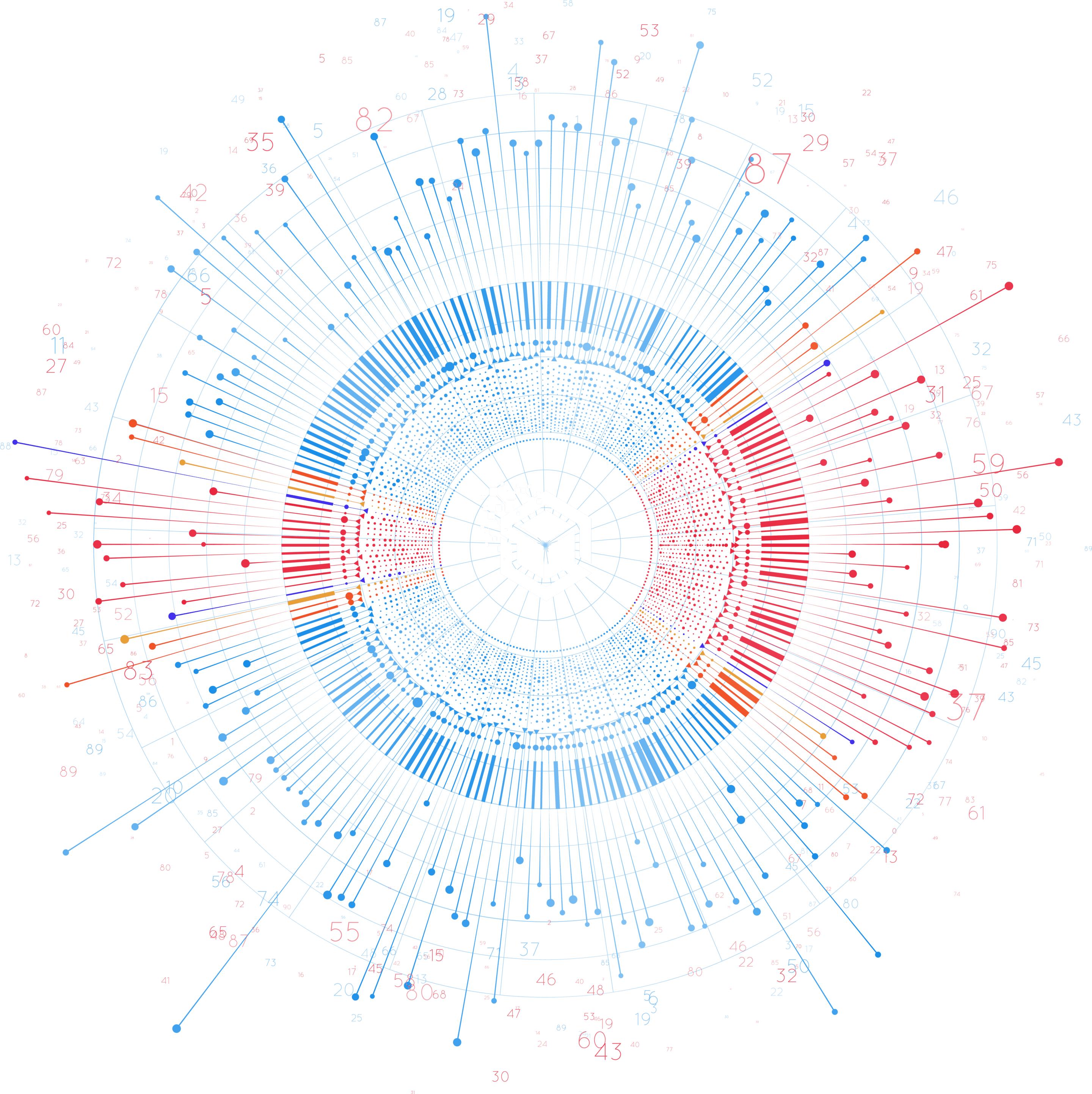
Our ENGAGEMENT PROCESS