Enterprise Incident Response solutions
Intelligence Driven Cyber Security Operations
Enterprise Incident Response
Incident response refers to the comprehensive process of addressing data breaches or cyberattacks, with the primary objective being the organization’s containment and control of the incident’s repercussions. The ultimate aim is to effectively manage incidents, thereby minimizing harm to systems and data, reducing recovery time and cost, and safeguarding the organization’s brand reputation.
To achieve this, organizations must establish a well-defined incident response plan, outlining the criteria for identifying a security incident and presenting a clear and straightforward process for teams to follow when dealing with such occurrences.
Furthermore, it is crucial for organizations to assign a dedicated team member or leader responsible for overseeing the entire incident response initiative and ensuring the successful execution of the plan. In larger organizations, this specialized team is typically known as the Computer Security Incident Response Team (CSIRT).
The importance of incident response plans is evident, yet a surprisingly large majority of organizations either lack one or possess an underdeveloped plan.
According to a survey, 75 percent of respondents admitted to not having a formal incident response plan consistently applied across their organization, with nearly half stating that their plan is either informal or nonexistent. Even among those with incident response plans, only 25 percent consider their initiatives to be “mature.”
These statistics are worrisome, particularly when considering that 35 percent of organizations report an increase in the time it takes to resolve cyber incidents, and 75 percent experience a rise in the severity of attacks they encounter.
The correlation between these statements is evident in the realm of cybersecurity, where speed plays a critical role in minimizing damage. The longer attackers can remain inside a target’s network, the more they can pilfer and disrupt. An effective incident response plan can limit the time attackers have by ensuring that responders comprehend the necessary steps and possess the required tools and authority to act promptly.
Incident Response Plan
An incident response plan is a comprehensive document outlining security procedures to be followed in the event of an incident, as well as identifying those responsible for incident response. Typically, an incident response plan includes the following key elements:
- Incident response methods and strategies.
- How incident response aligns with and supports the broader mission of the organization.
- Specific activities and actions required for each stage of incident response.
- Roles and responsibilities assigned to individuals for carrying out incident response activities.
- Communication channels established between the incident response team and the rest of the organization.
- Metrics and criteria used to evaluate the effectiveness and efficiency of incident response efforts.
The benefits of an incident response plan extend beyond the resolution of a cybersecurity incident. The plan continues to provide support for legal purposes, serving as documentation to be submitted to auditors. Moreover, it offers a valuable historical reference that can enhance responses to similar incidents in the future.
Cyber Defence
Our approach to enterprise incident response
Initial Meeting
We will formulate an agreement outlining responsibilities and procedures between both parties. It defines roles, communication protocols, and response timeframes, ensuring coordinated and efficient incident resolution.
Initial Detection and Analysis
As soon as the incident is detected in managed SIEM our team will start working on the IOC. Our Analysts review alerts, identify indicators of compromise (IoC), and use them to triage the threat. Our team will often perform additional testing, reviewing related alerts and ruling out false positives to get a complete picture of suspicious events.
Incident Prioritization
Our response team will understand the impact of security incidents on the organization’s business activity and valuable assets.
Notify
Our incident responder notifies the appropriate people within the organization. In case of a confirmed breach, organizations typically notify external parties, such as customers, business partners, regulators, law enforcement agencies, or the public. The decision to notify external parties is usually left to senior management.
Containment and Forensics
Our Incident responders act promptly to halt the incident and safeguard the environment against reinfection. Additionally, they gather forensic evidence, as required, for subsequent investigations or potential legal actions.
Recovery
Our Incident responders first eliminate malware from the impacted systems, followed by rebuilding and restoring the systems from backup to bring them back to their normal functioning state. Additionally, they apply necessary patches to enhance security and prevent future incidents.
Incident Review
In order to prevent the recurrence of incidents and enhance future responses, the response team conducts a thorough review of the events leading to the detection of the recent incident. They analyze successful aspects of the incident response, identify opportunities to enhance systems (including tools, processes, and staff training), and propose remedies for any vulnerabilities found.
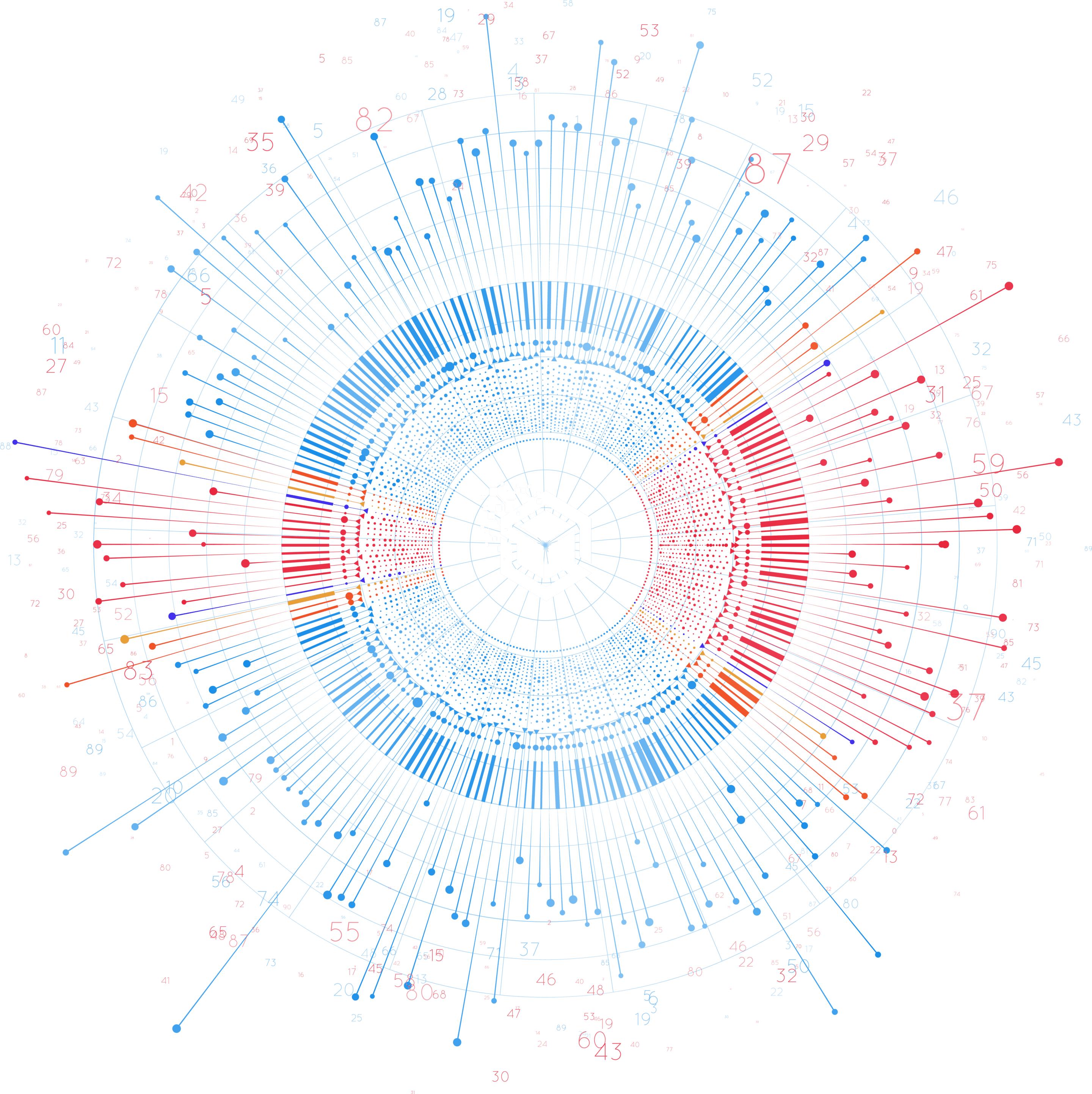
Our CSIRT Team Structure
The incident response team consist the following key roles:
- Incident Response Manager (Team Leader): Coordinates team actions and ensures a focus on minimizing damages and swift recovery. Prioritizes actions during incident isolation, analysis, and containment, providing guidance during high-severity incidents.
- Security Analysts: Assists the manager, working across departments to identify and rectify security flaws in systems, solutions, and applications. Recommends measures to enhance overall security.
- Lead Investigator: Isolates the root cause, analyzes evidence, manages other security analysts, and facilitates rapid system and service recovery.
- Threat Researchers: Provide incident context and threat intelligence, creating a database of internal intelligence using information from previous incidents. Automated threat intelligence tools may complement their role.
- Communications Lead: Communicates with internal and external stakeholders, including management, legal, press, customers, and other relevant parties.
- Documentation and Timeline Lead: Documents the team’s investigation, discovery, and recovery efforts, creating incident timelines for each stage. Advanced Security Information and Event Management (SIEM) systems can automate this process.
- HR/Legal Representation: Provides guidance in cases where incidents may escalate to criminal charges, ensuring compliance with legal requirements and protecting the organization’s interests.