Cyber Crisis Management Plan Services
Intelligence Driven Cyber Security Operations
Cyber Crisis Management Plan
Cyber crisis management plan is a comprehensive strategy designed to guide an organization’s response and actions during a cyber incident or data breach. It outlines the step-by-step procedures, roles, and responsibilities of key personnel in handling cyber threats effectively and efficiently. This plan covers various potential cyber crises, such as malware infections, unauthorized access to sensitive information, denial-of-service attacks, and other cybersecurity incidents. The goal is to mitigate the impact of the crisis, minimize the damage, and swiftly recover normal operations. The plan typically involves incident identification and classification, immediate containment and isolation of the threat, forensic investigation, communication protocols with stakeholders, and recovery measures. A well-prepared cyber crisis management plan is essential for organizations to respond swiftly, protect their data and reputation, and ensure business continuity in the face of cyber threats. Regular testing and updating of the plan are crucial to adapt to evolving cyber risks and maintain an effective cybersecurity posture.
The Cyber Crisis Management Plan offers a strategic framework and prescribes actions to proactively prepare for, respond to, and initiate recovery from a security breach. This plan encompasses various types of cyber crises, with a focus on understanding their potential targets and impact on the organization. It delineates the actions and responsibilities of relevant stakeholders and facilitates coordination among multiple departments and divisions within the organization. Moreover, the plan outlines how critical infrastructure owners should handle cyber crisis situations. Given the technology-intensive nature of the cybersecurity field, with new vulnerabilities arising as technology advances, organizations face new challenges daily. Thus, a cyber crisis management plan becomes imperative for investigating, detecting, protecting, and recovering from security attacks efficiently.
Managed Security
Our approach to CYBER CRISIS MANAGEMENT PLAN
IDENTIFYING THE PROBLEM STATEMENT
The problem statement in a cyber crisis management plan typically highlights the key issues and challenges the organization faces in effectively responding to and managing cyber incidents. It helps to identify the main problem areas that the plan aims to address. Here’s an example of a problem statement for a cyber crisis management plan.
DEVELOPING A COMMUNICATION PLAN
The communication plan helps ensure timely, accurate, and consistent information dissemination during a cyber incident. It involves defining the communication strategy, roles and responsibilities of communication team members, and methods of communication.
CREATE RESPONSE PROCEDURES
The response procedures involve a series of steps that guide the organization’s incident response team in detecting, assessing, containing, and recovering from cyber crises.
CONDUCTING DRILL EXERCISES
Drill exercises in a cyber crisis management plan are essential to test the effectiveness of the plan, assess the readiness of the incident response team (IRT), identify gaps, and improve the organization’s overall cyber resilience. These exercises simulate various cyber crisis scenarios, allowing the team to practice their response procedures in a controlled environment.
REVIEW AND UPDATE THE PLAN
To maintain the effectiveness and relevance of the cyber crisis management plan, regular reviews and updates are essential. The process should involve a comprehensive assessment of the plan’s components, response procedures, communication strategies, and incident response team readiness.
In What way can we be
CCMP PURPOSE
Certcube labs helps businesses to follow a systematic process to prepare, respond and coordinate against a security incident or a crisis situation .The primary purpose of CCMP is to provide secure data transmission by using the Advanced Encryption Standard (AES) algorithm in combination with cryptographic techniques like Cipher Block Chaining (CBC) and Message Authentication Code (MAC).
CCMP MANDATE
We prepare cyber crisis management plans as the regulatory authority requirements. We equip organizations to implement and ensure that compliance.The adoption of CCMP is driven by industry best practices and security standards set by organizations such as the Wi-Fi Alliance and the IEEE. Wi-Fi Alliance recommends the use of WPA2 or WPA3 with CCMP encryption for modern Wi-Fi networks.
CCMP STRUCTURE
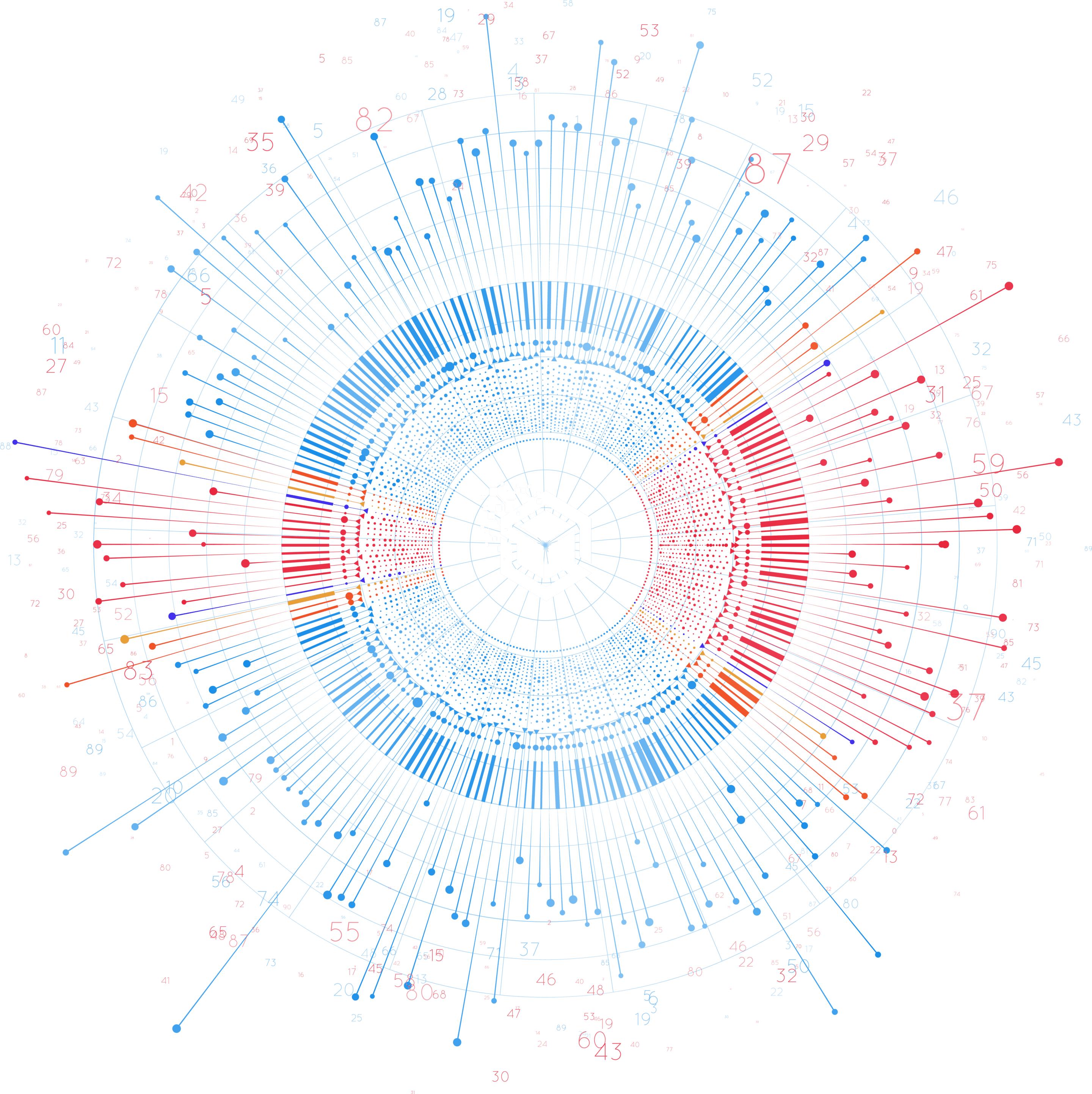
The structure of CCMP includes understating the nature of Crisis and contingencies , mind mapping the threat landscape ,Crisis recognition , building the cyber security capabilities , Incident prevention countermeasures , Post Incident activity to prepare for the future risks
CCMP POINT OF ACTION
Organisations should develop a crisis management committee for outlining roles and responsibility of stakeholders in CCMP coordination process . Our Team plays a key role as supportive Cyber Crisis management unit for your organisation and can help in building the robust crisis management Plan.